Your employees probably see more phishing emails than they report. Even in organizations with clear protocols, the majority of suspicious messages never make it to the IT security team. This gap is not because employees do not care or lack training. It is because the reporting process itself creates friction that stops people from following through.
When someone spots a sketchy email, they often hesitate, second-guess themselves, or simply cannot remember how to flag it. The result? Threats fly under the radar while IT teams operate with incomplete information.
Key Takeaways
- Most phishing emails go unreported due to friction in the reporting process, not lack of awareness.
- Fear of looking foolish or wasting IT time stops employees from flagging suspicious messages.
- Complicated or unclear reporting tools lead to abandoned reports and missed threats.
- Building a blame-free reporting culture increases threat visibility and strengthens security.
- Regular microlearning reinforces reporting habits and keeps cybersecurity top of mind.
The Reporting Gap in Cybersecurity
Organizations invest heavily in email security filters and threat detection systems, but these tools cannot catch everything. The human layer remains the last line of defense, yet studies consistently show that employees report only a fraction of the phishing attempts they encounter.
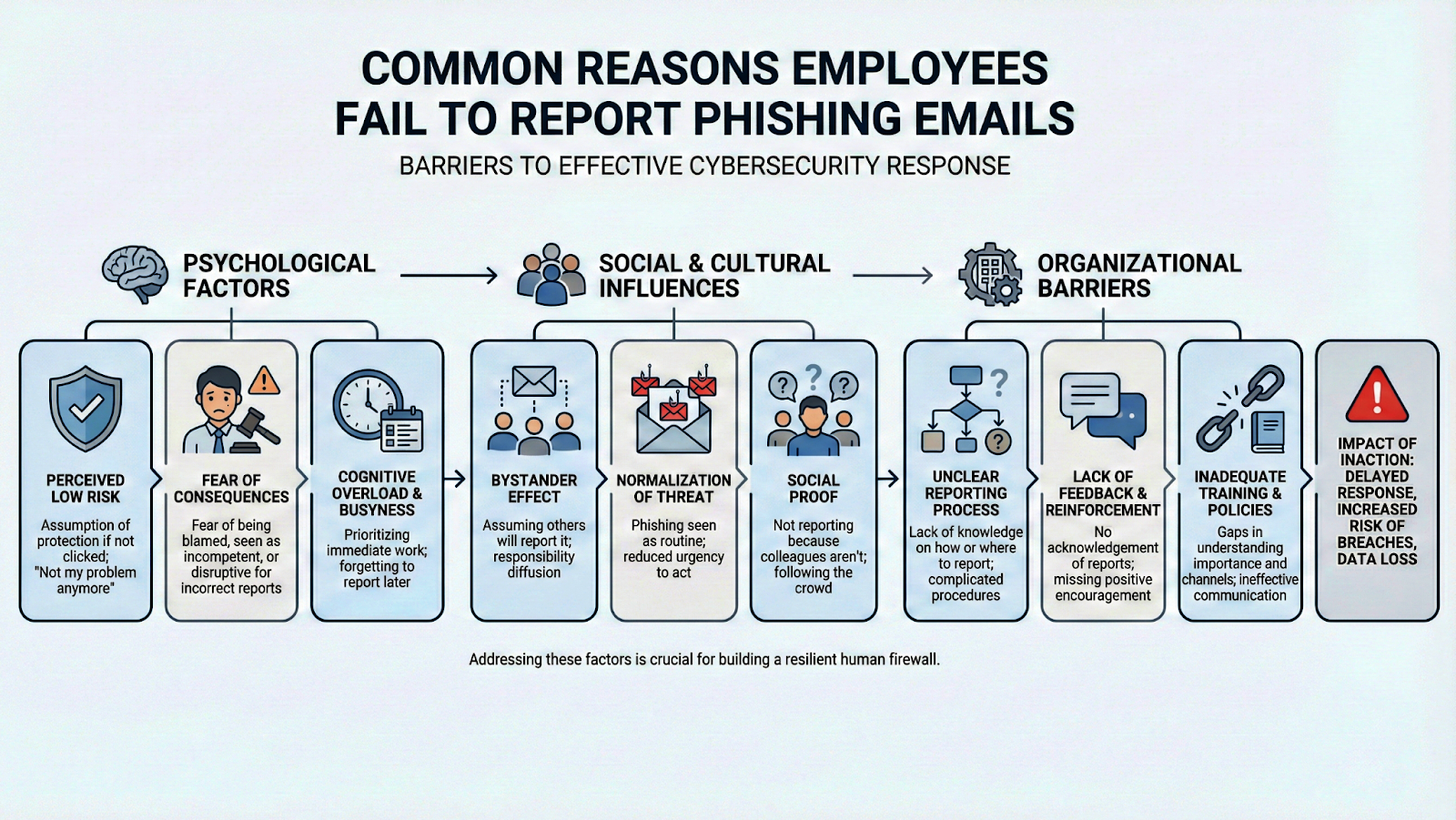
Research on barriers to reporting phishing emails reveals that even employees who recognize a phishing attempt often choose not to report it. This creates a dangerous blind spot where security teams cannot see the full scope of attacks targeting their organization.
The gap between detection and reporting matters more than most people realize. When IT does not know about an attempted attack, they cannot block similar messages, warn other employees, or adjust security protocols. Each unreported phishing email represents lost intelligence that could have protected others.
Common Barriers That Stop Employees From Reporting
Several factors conspire to keep phishing reports from reaching IT. Many employees genuinely do not know how to report a suspicious email. They might remember hearing about it during onboarding but cannot recall the specific steps when a questionable message lands in their inbox.
The human factors in cybersecurity reporting play a significant role here. People are more likely to delete suspicious emails and move on rather than spend time figuring out reporting procedures.
Fear is another major barrier. Employees worry about looking paranoid if they report something legitimate, or they are afraid of wasting IT time with false alarms. This anxiety is particularly strong in workplace cultures where mistakes are criticized rather than treated as learning opportunities. Some employees also assume that if a phishing email made it past the spam filters, it must be legitimate.
Top 7 Cybersecurity Mistakes Employees Make Without Knowing
Technical Hurdles in the Reporting Process
Even motivated employees hit roadblocks when they try to do the right thing. Many organizations use reporting tools that require multiple steps, special plugins, or access to specific portals.
If someone has to stop what they are doing, open a new application, copy message headers, and fill out a form, they might just delete the email instead. Organizations that provide clear guidance on how to download phish report data make it easier for teams to track and analyze threats.
The timing issue compounds these technical problems. Phishing emails often arrive when people are busy, distracted, or rushing between tasks. A complicated reporting process competes with deadlines, meetings, and the constant pull of daily responsibilities.
By the time someone has a free moment, the suspicious email sits forgotten in their inbox. Strong phishing platform capabilities can simplify this process and capture reports that would otherwise be lost.
Building a Culture That Encourages Reporting
The solution starts with culture, not technology. Employees need to feel safe reporting anything that seems off, even if they are wrong. Organizations that celebrate reports rather than dismiss them see higher participation rates.
When someone flags a legitimate email by mistake, the response should be gratitude for their vigilance rather than criticism. Incorporating employee onboarding training to spot cyber attacks sets the tone early and establishes reporting as a normal part of the job.
Regular communication helps too. IT teams should share sanitized examples of phishing attempts that employees reported, along with what would have happened if those emails had been clicked. This feedback loop shows people that their reports matter and helps them recognize similar threats in the future. Recognition programs that acknowledge employees who report suspicious activity can also shift attitudes over time.

Whale Phishing Understanding CEO Fraud in Cybersecurity
Strengthening Your Organization Response
Beyond culture, organizations need solid processes to handle the reports they do receive. The importance of organizational incident response plans cannot be overstated. When employees see that their reports lead to visible action, they are more likely to report again. Silence makes people wonder if anyone even read their submission.
Training plays an ongoing role in keeping reporting top of mind. Annual compliance modules are not enough because people forget. Short, frequent reminders that reinforce what to look for and how to report work better than lengthy sessions that happen once a year. Microlearning approaches deliver small bits of information regularly, building habits that stick rather than knowledge that fades.

If your organization struggles with low phishing report rates, it might be time to rethink your approach. A fully managed security awareness training program can help you build the habits and culture needed to close the reporting gap and keep your team protected.
Conclusion
Phishing continues to work because it exploits human behavior instead of technical weaknesses. When employees don't flag suspicious messages, companies miss critical visibility into the risks slipping past their defenses. Fixing that blind spot isn't solved by tighter rules or stronger spam blockers alone. It depends on easy ways to report incidents, a workplace that encourages speaking up, and ongoing education that keeps security habits active.
Every reported phishing email, whether it turns out to be malicious or not, represents an employee who felt confident enough to speak up. That confidence does not happen by accident. It is built through consistent reinforcement, positive feedback, and processes that make doing the right thing easy. When reporting becomes second nature, IT teams gain the visibility they need to protect the entire organization.









