Every year, as W-2s start landing in inboxes and employees begin thinking about refunds, cybercriminals get to work. Tax filing season is one of the most predictable windows for phishing attacks, and the reason is simple: people are already expecting financial emails. That expectation makes them much easier to deceive. Organizations that handle payroll data, HR records, and employee tax forms are especially at risk, and the attacks are getting harder to detect with each passing year.
Key Takeaways
- W-2 and payroll phishing attacks consistently spike during tax season because employees are already expecting sensitive financial communications.
- Criminals use both email and phone calls together to make their scams more convincing and much harder to dismiss.
- HR staff, payroll teams, and executives are the most frequently targeted employees in these types of campaigns.
- A single successful phishing attack can expose the Social Security numbers and tax data of every employee in an organization.
- Regular phishing simulations and ongoing security training are the most effective defenses against tax season phishing attacks.
Why Tax Season Creates the Perfect Storm
Tax season removes one of phishing's biggest obstacles: the element of surprise. Normally, an employee might pause before clicking a link in a message claiming to be from payroll. But between January and April, emails about W-2s, direct deposit updates, and tax forms are completely routine. Criminals know this, and they design their attacks to blend seamlessly into a season when financial communication is expected and constant.
The IRS has repeatedly warned businesses about W-2 phishing scams, where attackers pose as executives or HR contacts and request employee tax documents directly. These requests often look legitimate. They arrive with spoofed email addresses, familiar company language, and just enough urgency to push someone into acting before they stop to verify.
How Payroll Phishing Actually Works
Most payroll phishing attacks follow a familiar pattern. A criminal researches a company, identifies an HR or payroll contact, and crafts a message that appears to come from someone in leadership. The message asks for a spreadsheet of W-2 data, a list of employee SSNs, or a change to direct deposit information. The recipient, thinking they're doing their job, sends the data over without a second thought.
Research on tax-related phishing campaigns shows these attacks are becoming more sophisticated every year. Criminals now incorporate realistic branding, urgent language, and spoofed sender addresses that are nearly identical to legitimate ones. Some campaigns also use malicious attachments disguised as tax documents. Once opened, those files can install malware or steal login credentials, giving attackers ongoing access long after the initial breach occurs.
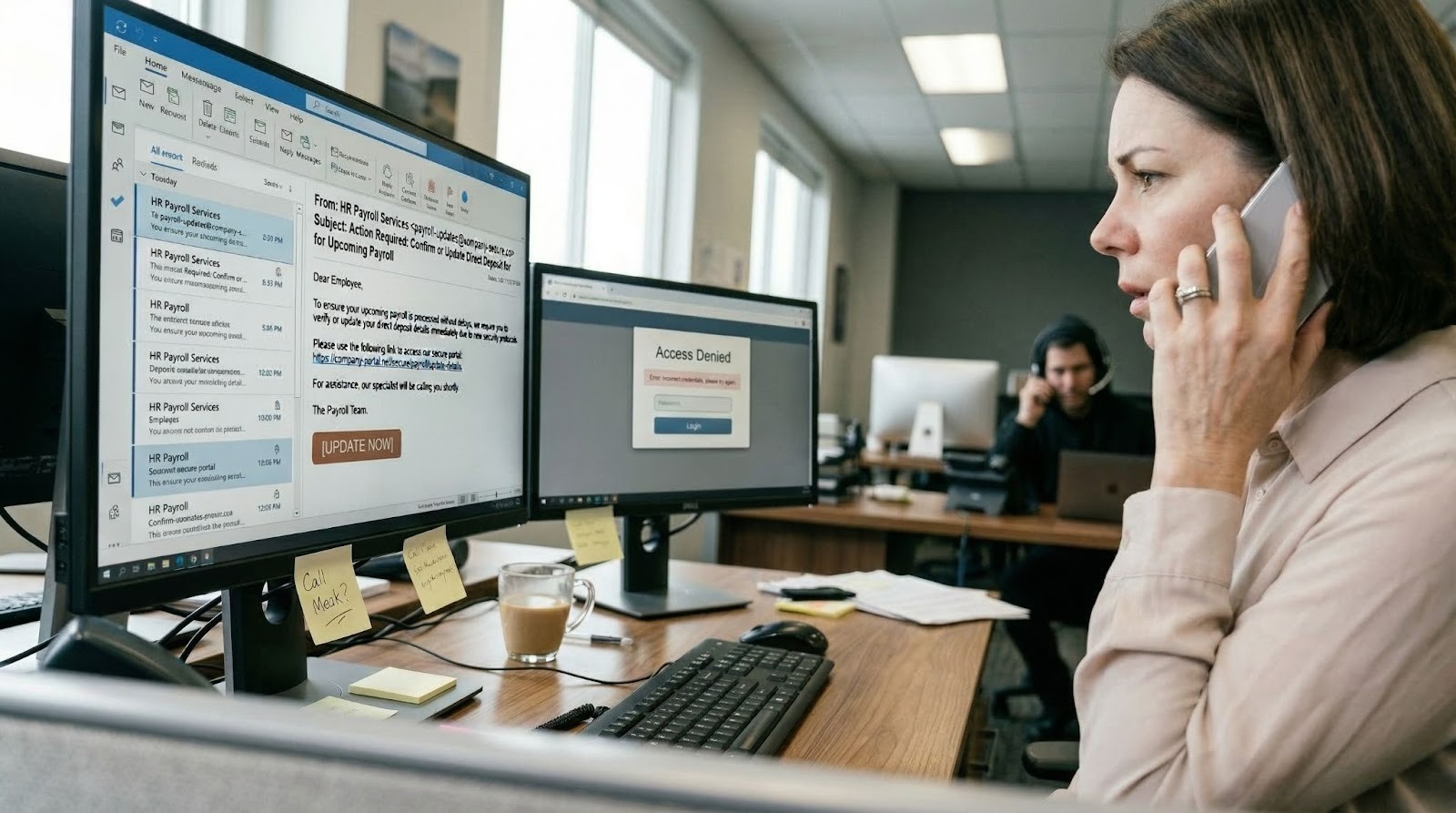
ALT Text: payroll employee experiencing dual-channel phishing attack combining a spoofed email and a vishing phone call
Whale Phishing: Understanding CEO Fraud in Cybersecurity
Criminals Use a Multi-Pronged Approach: Phone Calls and Emails
One of the more alarming trends in recent years is how attackers have moved well beyond email alone. Many now follow up their phishing emails with a phone call, and sometimes they call first just to set the stage. The call acts as social proof. An employee who receives an email from what looks like the CEO, followed by a call from someone claiming to confirm the request, is far more likely to comply than someone who only got the email.
This two-channel approach is especially effective against payroll staff because it closely mirrors how real urgent requests often work inside organizations. Criminals lean on the authority of the supposed caller, the time pressure of tax deadlines, and the familiar format of the request to make everything feel routine. Payroll phishing during tax season has increased sharply in part because this email-plus-phone combination is far harder to identify as fraud before it's too late.
The calls also serve as a form of vishing, where the attacker collects details about the target to make the follow-up email more convincing. By the time the phishing message arrives, the employee already has a name, a context, and a level of familiarity that lowers their guard.
Who Gets Targeted and Why
HR and payroll staff are the most obvious targets because they have direct access to W-2 data, direct deposit settings, and employee records. But executives face equal or greater risk. Whale phishing tactics, where criminals impersonate or specifically target high-level leaders, are common during tax season because executive authority can be used to push fraudulent requests through before anyone thinks to question them.
Finance teams, tax preparers, and accounting staff are also high-risk. Anyone who touches sensitive employee data or payroll systems is a potential entry point. The damage from one successful attack can be extensive, exposing hundreds or thousands of employees' personal and financial information at once.

ALT Text: IT security team conducting phishing simulation training with employees during a corporate security awareness session
What Your Organization Can Do Right Now
Awareness is a good foundation, but employees need to practice spotting attacks before they encounter a real one. Running phishing attack simulations training is one of the most effective ways to build that skill. Simulations expose people to realistic scenarios, show them what red flags to watch for, and help develop habits that last, especially when paired with clear, immediate feedback after each exercise.
Organizations that lack the internal resources to manage this consistently can benefit from fully managed security awareness training, which handles ongoing delivery, tracking, and reporting so your entire team stays prepared throughout the year rather than just during tax season.
Strong policies matter just as much as training. Any request to send W-2 data or change direct deposit information should require a secondary confirmation through a known, trusted channel. Replying to the original email alone is never a sufficient check.
Before the next tax season ramps up, make sure your team is ready. Start building phishing awareness with Drip7's simulations and give your employees the practice they need to recognize and report attacks before they cause damage.
Employee Onboarding Training: New Hires to Spot Cyber Attacks
Tax Season Won't Slow Down, and Neither Will Attackers
Phishing attacks tied to tax season aren't going away. Criminals are getting more patient, more precise, and more creative in how they combine tactics. The good news is that training works. Organizations that invest in regular, realistic security awareness programs consistently see fewer successful attacks because their employees know what to watch for.
The window to prepare may feel narrow, but preparation doesn't have to be seasonal. Year-round training keeps your team sharp no matter the time of year, and that consistent readiness pays off exactly when it matters most.









