Your company has invested in security training. Employees have sat through presentations, watched videos, and passed quizzes. Yet when the next phishing simulation rolls around, a surprising number still click the malicious link. It's frustrating, and it raises a real question: why does this keep happening? The answer isn't that employees are careless. The reality is far more complex, rooted in how our brains work, how we approach training, and the tactics attackers use to catch people off guard.
Key Takeaways
- Phishing attacks exploit psychological triggers like urgency, authority, and fear rather than technical ignorance.
- Annual training sessions fail because people forget most of what they learn within weeks.
- Busy employees make quick decisions without fully analyzing suspicious messages.
- Attackers constantly update their tactics, making yesterday's training less effective today.
- Consistent, bite-sized learning reinforces security habits better than one-time programs.
The Psychology Behind the Click
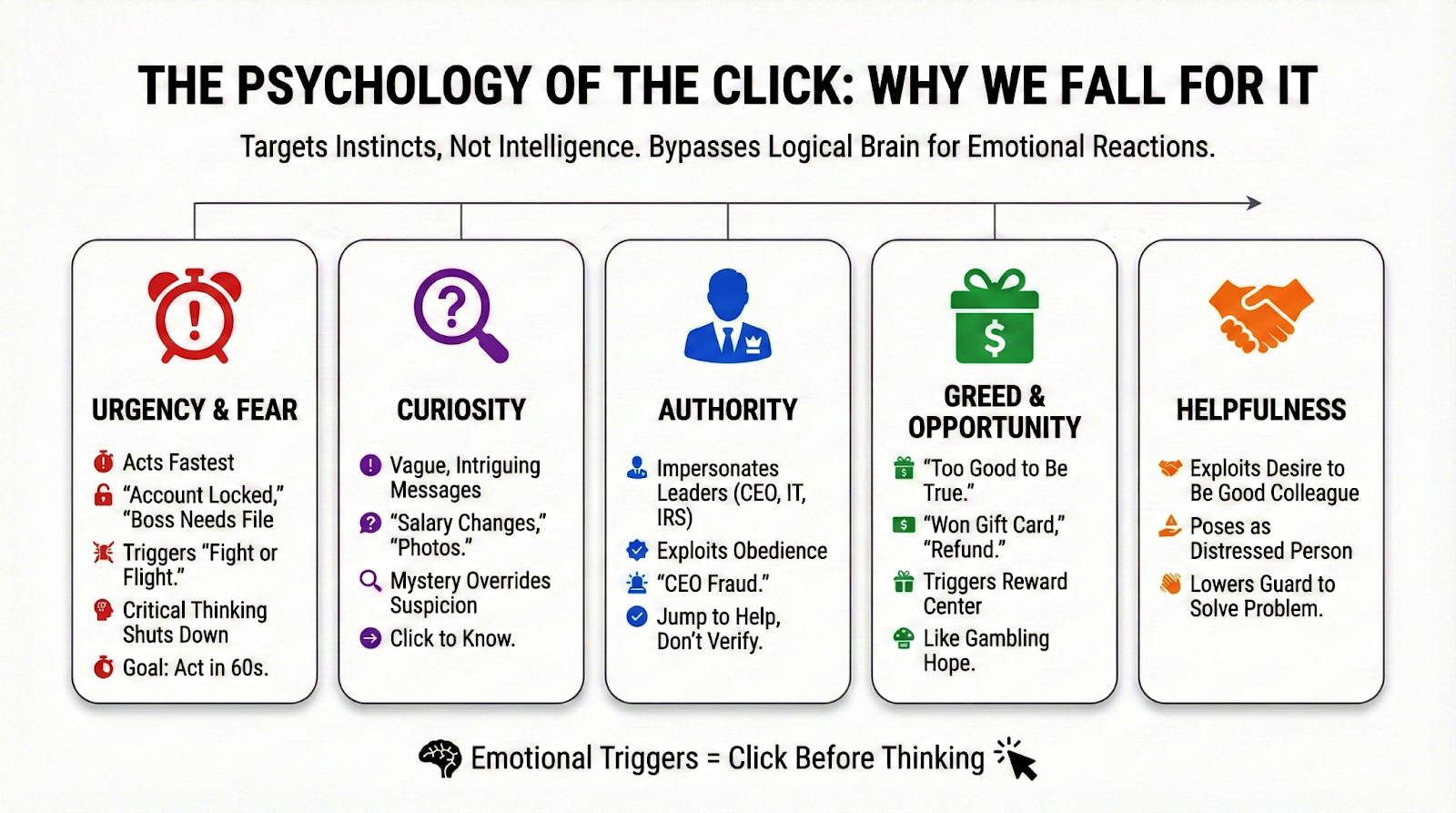
Phishing works because it targets how humans naturally respond to certain stimuli. When an email claims your account will be suspended or your boss urgently needs you to review a document, your brain shifts into reactive mode. This is where the psychological reasons people fall for scams become clear. Attackers craft messages that trigger emotions like fear, curiosity, or the desire to help, all of which bypass the logical part of your brain that would normally pause and evaluate.
Authority plays a huge role too. An email that appears to come from the CEO or IT department carries weight. People don't want to ignore their leadership or cause problems by questioning what seems legitimate. Scammers know this and exploit it ruthlessly. They impersonate trusted figures because it works, and it works because we're wired to comply with authority.
How Impactful is Interactive Cyber Security Training
Why Traditional Training Falls Short
According to phishing simulation failure rate research, industries across the board struggle with employees clicking on simulated attacks, even after completing awareness programs. The problem isn't that the training itself is bad. It's that human memory doesn't retain information well when it's delivered in one large dose and forgotten for months.
Think about how you learned to drive. Nobody handed you a manual, tested you once, and expected you to be road-ready forever. You practiced repeatedly over time, building habits and muscle memory. Security awareness works the same way. When training happens once a year, employees absorb some information but quickly lose most of it. By the time a real phishing attempt arrives, the lessons have faded.
This is exactly why organizations are shifting toward fully managed security awareness training that delivers consistent, ongoing education. Short, frequent lessons keep security top of mind without overwhelming employees or eating into their workday.
The Overloaded Inbox Problem
Your average employee receives dozens, sometimes hundreds, of emails daily. They're juggling meetings, deadlines, and endless notifications. When a phishing email lands in that chaotic mix, the recipient often makes a split-second decision based on surface-level details. The email looks official, the request seems reasonable, and they don't have time to scrutinize every message.
The human factor in cybersecurity incidents remains the biggest vulnerability in most organizations. It's not because people don't care about security. They're simply operating under cognitive overload, making decisions on autopilot while trying to get through their day. Attackers understand this and time their messages to hit when defenses are lowest, like early Monday mornings or late Friday afternoons.

Building a Cyber-aware Culture Why Training on Once a Year Isnt Enough
Attackers Never Stop Adapting
The phishing emails from five years ago look nothing like today's attacks. Criminals have access to sophisticated tools, AI-generated content, and personal information scraped from social media. They craft messages that mirror legitimate communications almost perfectly, complete with correct logos, formatting, and personalized details that make the deception convincing.
Training that focused on spotting obvious spelling errors or suspicious sender addresses doesn't prepare employees for these advanced threats. Modern phishing uses clean language, legitimate-looking domains, and context-aware content. An employee trained to look for broken English won't catch a polished scam that references a real project they're working on.
What Actually Works to Reduce Failures
The most effective approach combines regular, practical training with realistic simulations. Implementing phishing attack simulations training helps employees experience attacks in a controlled environment where mistakes become learning moments instead of breaches. When someone clicks on a simulated phishing link, they get immediate feedback that reinforces the lesson far more effectively than a PowerPoint slide ever could.
Frequency matters just as much as quality. The brain needs repeated exposure to information before it sticks. Short training sessions delivered consistently, even just a few minutes each week, build lasting habits. Employees start recognizing suspicious patterns automatically because they've been practicing regularly, not because they memorized a checklist months ago.

Organizations also benefit from clear policy workflows that give employees a straightforward process for reporting suspicious messages. When people know exactly what to do when something feels off, they're more likely to pause and verify rather than click and hope for the best.
Take the Next Step
If your current training program isn't moving the needle on phishing test results, it might be time for a different approach. See how phishing simulation training can transform your security culture and turn your employees from vulnerabilities into your first line of defense.
Building a Stronger Human Firewall
Employees fail phishing tests not because they're negligent but because they're human. Our brains respond predictably to certain triggers, and attackers have gotten very good at exploiting those responses. The solution isn't to blame the workforce or pile on more mandatory training that nobody remembers. It's to work with human psychology instead of against it, using frequent reinforcement, realistic practice, and clear procedures that make the right choice the easy choice.
When organizations commit to ongoing, engaging security education, failure rates drop and real incidents decline. That shift starts with understanding why people click in the first place and building programs designed to address those root causes. The goal isn't perfection. It's progress, and with the right tools, that progress adds up to meaningful protection.









