Every year, tax season brings a predictable surge in cyberattacks targeting businesses of all sizes. Finance and HR teams are processing W-2s, routing payroll data, and sharing sensitive financial records under tight deadlines, and criminals use that distraction deliberately. A tax-related data breach doesn’t just affect one file or one employee. It can ripple through an entire organization, damaging finances, compliance standing, and client trust in ways that take years to fully repair.
Key Takeaways
- Tax season is one of the highest-risk periods for data breaches because attackers exploit the surge in sensitive financial data being processed.
- Criminals frequently use a coordinated approach that pairs phishing emails with follow-up phone calls to pressure employees into complying.
- The average cost of a data breach now exceeds $4 million, with tax-related incidents often carrying additional regulatory penalties.
- Reputational damage after a breach can take years to recover from and directly affects client retention and long-term revenue.
- Consistent employee training is one of the most cost-effective ways to reduce the risk of a successful attack during tax season.
How Tax Season Creates a Target-Rich Environment
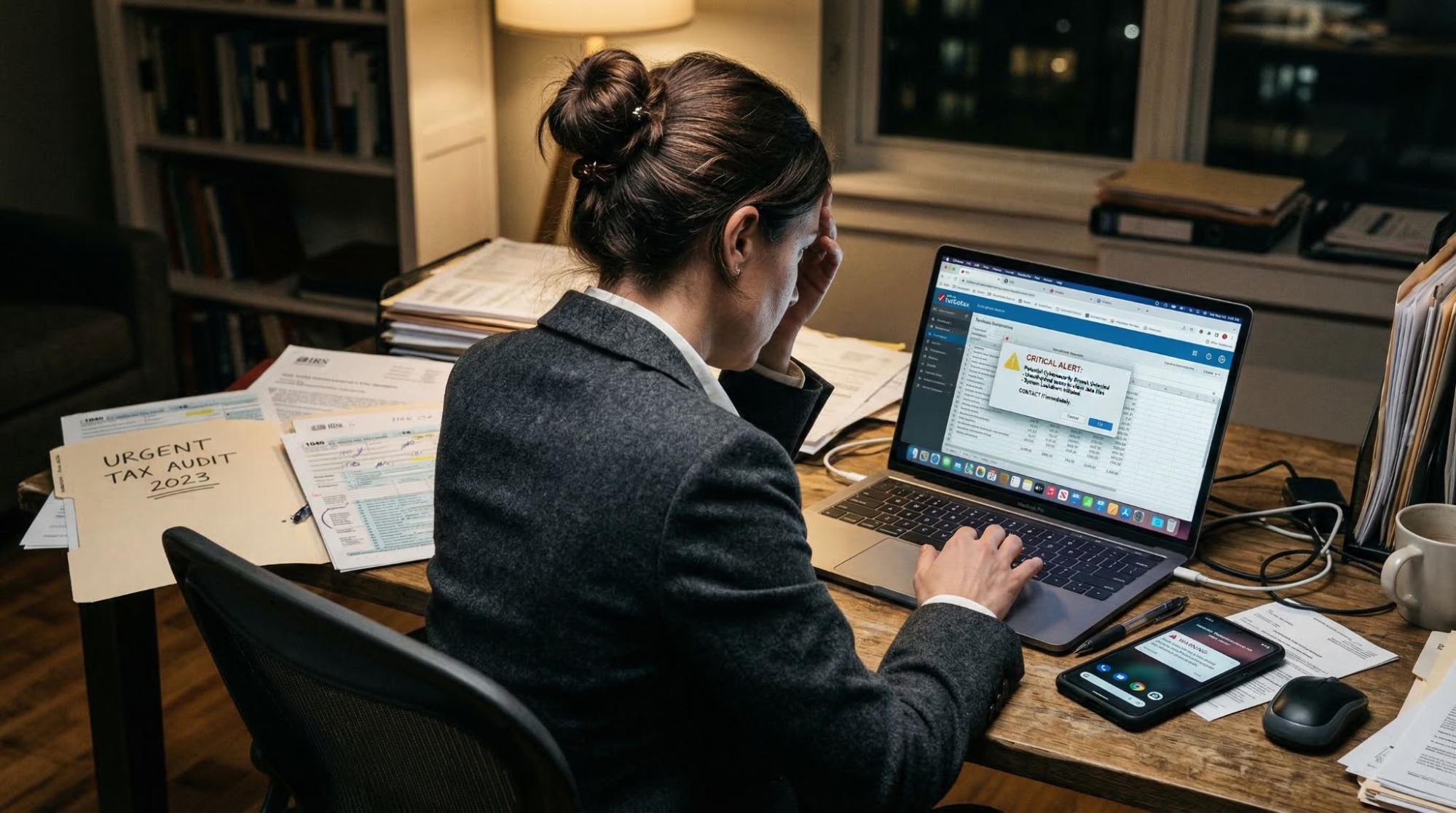
Tax season creates a perfect storm for attackers. Finance and HR teams are handling high volumes of sensitive data while racing against deadlines, and criminals time their moves deliberately around those pressure points. They target payroll runs, W-2 distribution windows, and quarterly filing dates because those are the moments when employees are too busy and too stressed to pause and question anything.
Phishing emails are still the most common entry point. Criminals impersonate the IRS, payroll vendors, accounting software providers, and even internal executives to make their messages look legitimate.
They study their targets, copy branding elements, and use urgent language designed to trigger action before critical thinking kicks in. One click on a malicious link can hand over login credentials, expose W-2 data for your entire workforce, or open a backdoor into your network.
The Multi-Pronged Attack: Phone and Email Working Together
What makes tax-related attacks especially effective is that criminals rarely stop at a single email. Many now use a coordinated strategy that layers phishing messages with follow-up phone calls, a tactic called vishing. The sequence is designed to feel like a real business interaction: an employee receives an urgent email from what appears to be payroll or a tax authority, then gets a call shortly after from someone claiming to verify the request.
This dual-channel approach works because it mirrors how real workplace processes unfold. An employee who hesitates after seeing the email becomes far more likely to comply once a professional voice confirms it on the phone. The caller references specific details from the original message, creates a sense of urgency, and uses calm, authoritative language to short-circuit doubt. By running both channels together, attackers dramatically raise their success rate and make the scam much harder to catch in the moment.
Organizations that invest in phishing attack simulations training give employees direct practice recognizing these exact scenarios before they encounter them for real. That repetition builds the kind of instinct that holds up even when someone is stressed or rushed, and it’s often the only thing standing between a smooth tax season and a serious security incident.

What a Tax-Related Breach Actually Costs
The financial damage from a tax-related breach accumulates fast. The average cost of a data breach now exceeds $4 million for most organizations, and that figure doesn’t fully capture the impact. Legal fees, forensic investigations, mandatory breach notifications, and regulatory fines all pile on top of each other. Tax-related breaches are particularly expensive because the stolen data, including Social Security numbers, direct deposit account details, and full compensation records, has long-term value on the black market.
The financial losses from data breaches extend well beyond immediate incident response. Depending on your industry, your business may face HIPAA violations, state-level data protection penalties, or IRS compliance failures tied to how taxpayer information was handled. These fines can accumulate quietly over months while regulators review what happened, and they often hit smaller organizations the hardest.
The ROI of Managed Cybersecurity Training Programs
Reputational Damage That Outlasts the Incident
The financial hit is serious, but the reputational fallout can be harder to recover from. Research on reputational damage after breaches consistently shows that clients, partners, and prospective employees lose confidence in organizations that fail to protect sensitive data. For businesses that manage payroll services, accounting, or financial records on behalf of clients, that trust is the foundation of the whole relationship. When it breaks, the damage goes deep.
Rebuilding a reputation takes sustained effort, transparency, and time, and some businesses never fully regain their footing. Clients quietly move to competitors, key employees start looking elsewhere, and the association with a known breach follows the brand for years. That’s why cybersecurity can’t be treated as just an IT concern. It’s a business continuity issue, and the cost of a breach is almost always higher than the cost of preventing one.

Why Traditional Cybersecurity Training Fails — and How to Fix It
Why Your People Are Both the Risk and the Solution
Most data breaches trace back to a human action: a click, a reply, a misdirected transfer. Technology controls matter, but they don’t eliminate the need for a trained workforce. The tactics attackers use during tax season, specifically the combination of email pressure and phone-based social engineering, are designed to bypass firewalls by going through people instead of around them. Training isn’t optional here. It’s a core part of your defense.
Organizations that implement fully managed security awareness training see measurable drops in phishing click rates and faster response times when real incidents occur. The data behind the roi of managed cybersecurity training programs supports what security teams already know: a trained workforce costs far less than the alternative. Keeping that training consistent throughout the year, not just before tax season, is what actually makes it work.
Your employees are your most reliable defense during tax season. Strengthen your team with Drip7’s fully managed security awareness training.
Conclusion
Tax-related data breaches aren’t accidents. They’re planned, timed, and engineered around the specific pressures of tax season. Criminals use phishing emails and phone calls together, exploit human psychology under deadline stress, and target financial data that businesses generate in high volumes at predictable times of year.
Getting ahead of this requires more than good software. It requires employees who can recognize the tactics, know how to respond, and stay sharp all year. Consistent training builds that awareness. When your people know what to look for, your business is genuinely harder to attack.