Business conferences are ideal targets for cybercriminals. The combination of professionals on shared networks and a trusting environment makes attendees vulnerable. Attackers exploit this by blending in, creating fake Wi-Fi, and using social engineering, often while posing as a harmless attendee to map security weaknesses.
Key Takeaways
- Conference environments create unique cybersecurity risks through shared networks and concentrated professional targets.
- Public Wi-Fi at events serves as an easy attack vector for man-in-the-middle attacks and data interception.
- Social engineering tactics become more effective when attackers physically mingle with targets at professional gatherings.
- Physical security lapses during conferences expose devices and credentials to theft or unauthorized access.
- Post-conference phishing campaigns exploit newly gathered contact information and event-specific trust relationships.
Why Conferences Are High-Risk Environments
Conferences are high-risk security environments. Attendees use unfamiliar networks, expose devices, and share data, prioritizing networking over security. Attackers exploit these lowered defenses and the false sense of security, thriving on the open, collaborative, and valuable nature of these events.
This setting, despite issues like badge fraud, is ideal for sophisticated threat actors targeting high-value professionals in finance, healthcare, or tech. Cybersecurity threats at business conferences have evolved beyond simple opportunistic attacks to planned campaigns designed to breach specific organizations.
The Public Wi-Fi Trap
Conference Wi-Fi is often insecure, yet attendees connect without concern. Attackers create deceptive rogue access points, like slight variations of legitimate network names. Connecting allows them to intercept all transmitted data—including banking credentials, emails, and remote company documents.
How attackers use public Wi-Fi at events demonstrates that even legitimate conference networks can be compromised. Man-in-the-middle (MITM) attacks occur when an attacker intercepts data between a device and the connection point, reading or altering it. This is highly effective in crowded conference halls due to bandwidth competition. Attackers only need a laptop and common software.
Whale Phishing Understanding Ceo Fraud in Cybersecurity
Your VPN offers some protection, but many people either don't have one configured on their devices or forget to activate it when they arrive. Some conferences even provide legitimate but unsecured networks, and there's no way to distinguish between safe and dangerous connections just by looking at available network names. The convenience of free, open Wi-Fi overrides security awareness for most attendees.

Social Engineering Gets Physical
Digital social engineering tactics become even more effective when the attacker is standing right next to you. Criminals infiltrate conferences for intelligence and system access by exploiting casual conversations and the trusting environment. Tactics range from photographing badges for impersonation (badge cloning) to aggressively posing as staff or fake vendors. These individuals install malware, capture credentials, or gather data under the guise of offering services like phone charging, prize scans, or device troubleshooting while attendees are distracted.
Device Security Falls Apart
Conferences pose significant security risks: unattended devices are vulnerable to malicious USBs, unauthorized restarts, or screen photography. Shoulder surfing easily steals passwords/data. Attackers also use "USB drops" infected, branded drives to compromise devices and corporate networks.
Pre-Conference Reconnaissance
Attackers research attendee lists, speakers, and social media weeks ahead, using platforms like LinkedIn and Twitter to find high-value targets and craft personalized attacks. Event-related social media posts are risky, advertising employees' absence and location. Sharing photos of badges or behind-the-scenes areas provides valuable security and access information to criminals.
Registration platforms themselves can be targets. Attackers compromise registration databases to harvest attendee information before the event even begins. They use this data to send convincing phishing emails that reference the specific conference, making their attacks more credible.

Top 7 Cybersecurity Mistakes Employees Make Without Knowing
Post-Conference Attacks
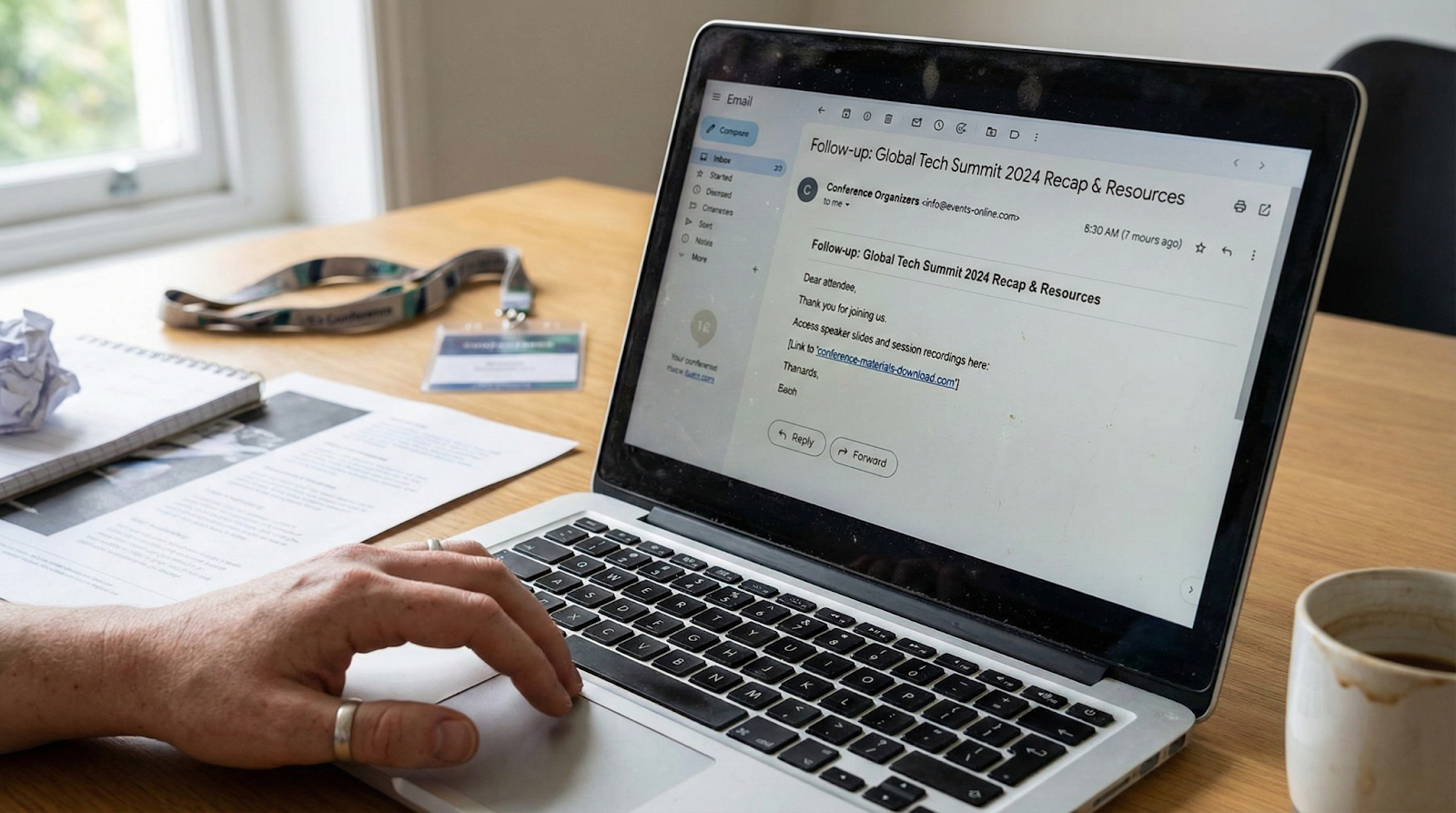
Post-conference, attackers leverage gathered information for follow-up campaigns. Phishing emails, disguised as surveys or networking requests, feel authentic by referencing event specifics. Malware surges, delivering infected documents disguised as presentation slides, attendee lists, or exclusive research. Your phishing attack simulations and training prepare teams to recognize these tactics, but the timing and context make these attacks particularly convincing.
Post-conference, Business Email Compromise (BEC) attempts rise. Criminals impersonate attendees, leveraging specific details (meetings, deals, connections) gathered from conversations or social media to make urgent requests for wire transfers or sensitive information seem authentic.
Building Conference-Ready Security Awareness
Protection starts before employees leave for the event. Organizations need clear policies about conference security that go beyond standard office protocols. Building a cyber-aware culture why training once a year isnt enough becomes obvious when you consider the unique threats conferences present.
Training should cover specific conference scenarios, not just general security principles. Employees need to understand why they shouldn't connect to open Wi-Fi networks, how to recognize social engineering in person, and what to do if they suspect their device has been compromised. Mobile cybersecurity training anytime anywhere ensures this knowledge stays accessible even when employees are away from their desks.
Mandatory pre-event security briefings for company attendees must cover specific risks based on the event type, location, and attendee profile. High-profile conferences demand stricter precautions than smaller, regional gatherings.
Practical Conference Security Measures
Implement simple technical controls: use VPNs, disable auto Wi-Fi, and install privacy screens. Use cellular hotspots instead of potentially hostile conference Wi-Fi. Maintain strong physical security: never leave devices unattended, use cable locks, and keep phones secure. Discuss sensitive information in private spaces only.
Follow post-conference protocols: assume all devices are compromised. Run security scans, change passwords, and monitor for suspicious activity. Be wary of unexpected post-event communications. Your team's security awareness determines whether conference attendance strengthens or compromises your organization's defenses. Strengthen your defense with targeted cybersecurity training that prepares employees for real-world threats they'll encounter at industry events.
Conclusion
Conferences are valuable for professional growth but remain prime targets for cybercriminals due to the concentration of industry professionals, relaxed security, and shared infrastructure. Organizations must recognize this risk and prepare teams by treating conference attendance as a high-risk activity requiring specific preparation, active vigilance, and thorough follow-up, rather than a security break.









