Tax season is one of the busiest times of year for HR departments and finance teams, but it's also one of the most active periods for cybercriminals. Every spring, attackers ramp up their efforts because they know employees are distracted, deadlines are tight, and sensitive financial data is moving fast. The combination of urgency and high-value information creates a perfect opening for scams, and employees are often the first line of defense.
Key Takeaways
- Tax season triggers a surge in phishing attacks targeting employees with fake IRS notices and payroll requests.
- Criminals often combine phone calls and emails to make their scams feel more convincing.
- W-2 phishing schemes can expose sensitive employee data and create serious financial and legal liability.
- Regular training helps employees recognize red flags before falling for social engineering tactics.
- Drip7's microlearning platform keeps cybersecurity awareness consistent year-round, not just during filing season.
Why Tax Season Brings More Cyber Threats
Tax filing season creates a predictable window of vulnerability for organizations of all sizes. Employees are handling W-2s, direct deposit changes, and tax-related documents constantly, which gives attackers a ready-made cover for their schemes.
A well-crafted phishing email referencing an IRS notice or payroll update can look completely routine when everyone is already thinking about taxes. Cybercriminals count on that, and they plan for it months in advance.
The stakes are higher during this period too. Tax-related phishing attempts don't just compromise individual accounts. They can expose employee records, trigger unauthorized wire transfers, and result in regulatory penalties. These scams have grown more targeted in recent years, partly because attackers have access to more personal data than ever.
Whale Phishing: Understanding CEO Fraud in Cybersecurity
The Scams Employees Need to Know About
IRS Impersonation Emails and Fake Notices
One of the most common tactics during tax season is IRS impersonation phishing, where attackers send emails designed to look like official IRS correspondence. These messages typically claim there's a problem with a tax filing, a refund is on hold, or that immediate action is needed to avoid penalties. The goal is to create panic and push the employee to click a link or hand over credentials before stopping to think.
One thing worth knowing: the IRS does not initiate contact through email, text messages, or social media. Any message claiming to be from the IRS and asking you to log in or provide personal information is a scam, regardless of how official it looks.
W-2 Phishing Schemes
W-2 phishing schemes are especially dangerous because they target HR and payroll staff directly. A scammer poses as a company executive and sends an internal-looking email requesting a full list of employee W-2 forms. The request often cites an upcoming audit or a last-minute filing deadline. Once payroll hands over that data, criminals can file fraudulent returns within hours.
This is also a textbook example of CEO fraud tactics, where impersonating a high-authority figure pressures employees into skipping standard verification steps.

ALT Text: Graphic showing a spike in cybersecurity threats during tax season with a calendar and a red alert icon
How Criminals Use a Multi-Pronged Approach: Phone Calls and Email
One of the most effective and underestimated tactics is when attackers combine multiple channels in a single scam. A criminal might send a phishing email, then follow up with a phone call impersonating IT support, the IRS, or an internal manager. The call makes the original email feel verified. When someone calls to confirm a request you just received by email, the instinct is to trust it.
This combination is harder to catch because it mimics how legitimate internal communication often works. Employees should know an IRS follow-up call doesn't validate an email on its own. Any ask for sensitive data or financial action should go through official verification channels, no matter how many touchpoints it came through.
What Employees Can Do Right Now
Training is the most reliable line of defense, and it doesn't have to be complicated. Employees should slow down before acting on any message that creates urgency, requests personal data, or involves financial transfers. Verifying requests through a separate channel, like calling a manager using a known number rather than one from the email, stops most attacks cold.
Organizations that invest in phishing attack simulations training give employees a chance to practice spotting these scenarios in a safe environment. Simulations work because they expose teams to realistic attack patterns without real consequences, building recognition and confidence over time.
It also helps to revisit the top 7 cybersecurity mistakes employees make as a team before tax season peaks. Common errors like reusing passwords, clicking before verifying, and dismissing security alerts spike under deadline pressure, and a timely refresher makes a measurable difference.
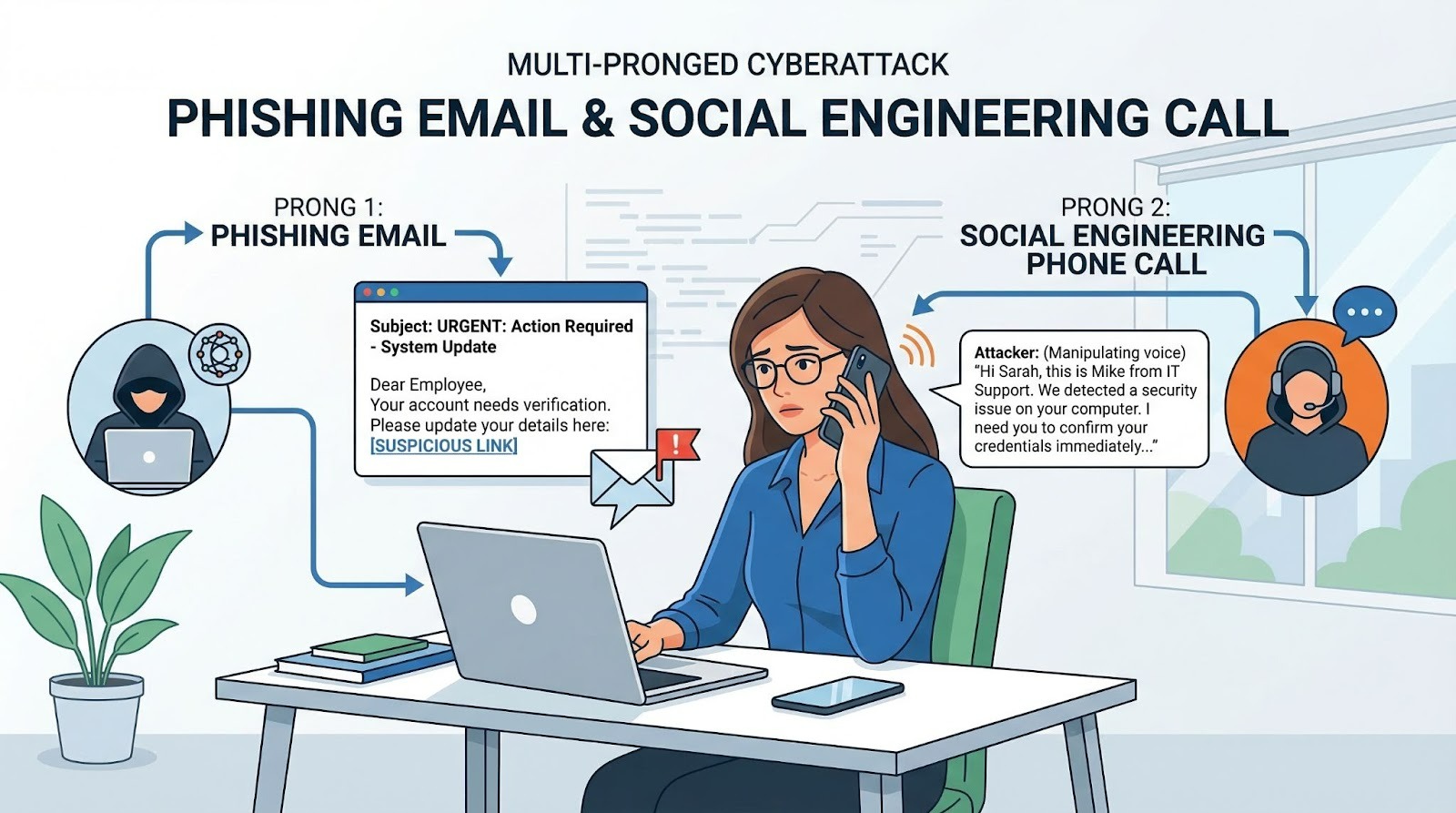
ALT Text: Split-screen illustration showing a phishing email and a scam phone call working together to deceive an employee
Employee Onboarding Training: New Hires to Spot Cyber Attacks
Why Annual Training Isn't Enough Anymore
A one-day cybersecurity session in January doesn't prepare employees for April's threats. Tactics evolve fast, and AI Phishing Scams Employees Fall for Instantly shows exactly how quickly things change. Today's criminals use AI to generate convincing emails, mimic writing styles, and build spoofed domains nearly identical to real ones. Employees trained months ago may not recognize what a modern phishing attempt looks like now.
Fully managed security awareness training delivered consistently throughout the year keeps employees sharp without burning them out. Drip7's microlearning platform sends short, targeted lessons employees can finish in minutes, building retention over time rather than cramming content they'll forget by next week.
If you want to see how prepared your team is against tax season threats, Drip7's phishing attack simulations are built to mirror the exact scams showing up in real inboxes right now. Getting started takes minutes, and the results give you a clear picture of where your team stands.
Stay Ready, Not Just Reactive
Tax season ends, but cybercriminals don't stop. The habits employees build now carry into the rest of the year, which is why timely, consistent training matters. Organizations that treat cybersecurity as an ongoing practice rather than a seasonal checklist come out with fewer incidents and stronger teams. The window for getting this right is open right now.









